Abstract
VTech's DigiGo is a hand held smart device for children. The device contains a chat application chatting with friends and family, called Kid Connect. The app has a broken certificate pinning implementation that allows a man in the middle attack on text sent by the chat app.
Tested versions
This issue was tested on a VTech DigiGo running firmware version 83.60630. It is likely that other versions are also affected.
Fix
VTech pushed a firmware update to address this issue on 6 November, 2017. The firmware version still displays as 83.60630.
Introduction
VTech's DigiGo is a hand held smart device for children. The device contains a chat application chatting with friends and family, called Kid Connect.
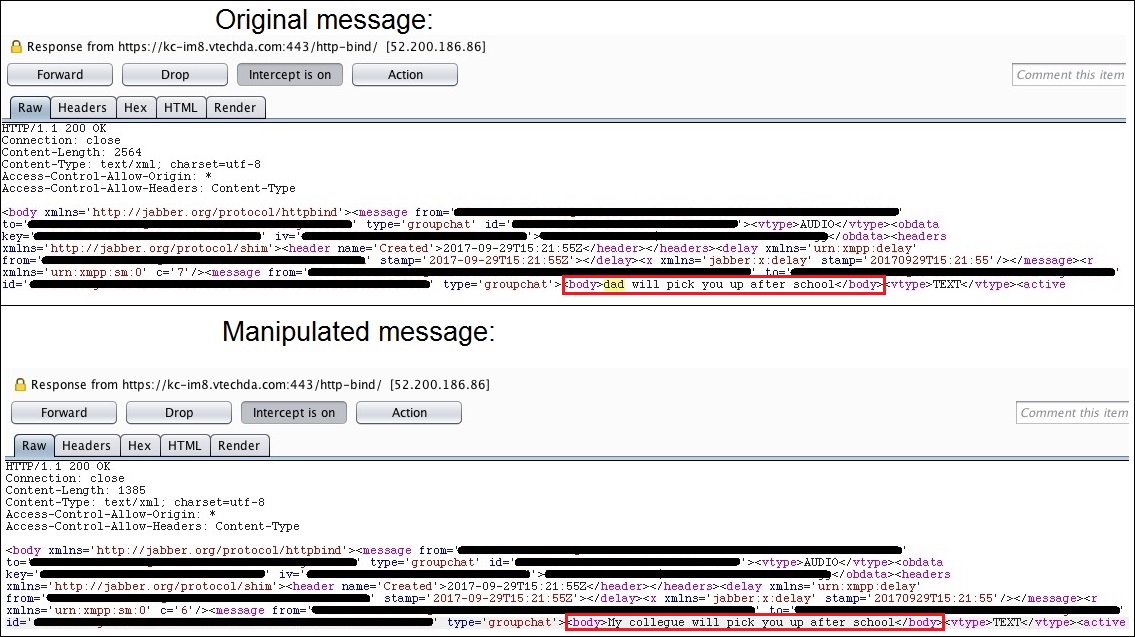
Certificate pinning is implemented to prevent an attacker from hijacking traffic from the chat app. Not all domains used for communication are pinned. TLS certificates that are not pinned are not validated, and allows an attacker to perform a man in the middle attack on the chat app. Hijackable data includes the login procedure and all text sent to and from the app.
Details
Kid Connect uses the Jabber protocol, and certificate pinning is used an extra security layer in its TLS traffic. Research indicated that the app implements pinning on the following domains:
- *www.vtechda.com
- kc-web.vtechda.com
- kc-proxy.vtechda.com*
Above domains don't include all domains that the app uses to communicate. The domain kc-im8.vtechda.com is used for authentication and sending text messages. This domain is not pinned, and the device doesn't seem to validate TLS certificates for domains not in the pinning list. An attacker can perform a man in the middle attack on the chat app and hijack the authentication procedure and text messages.
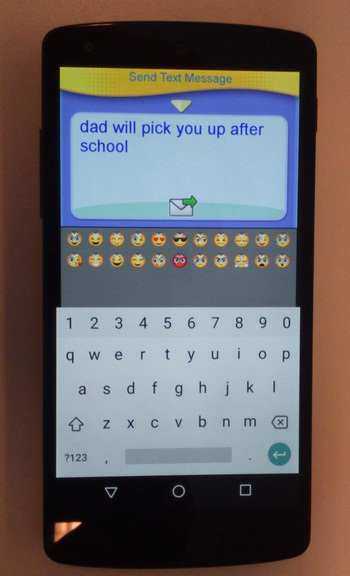
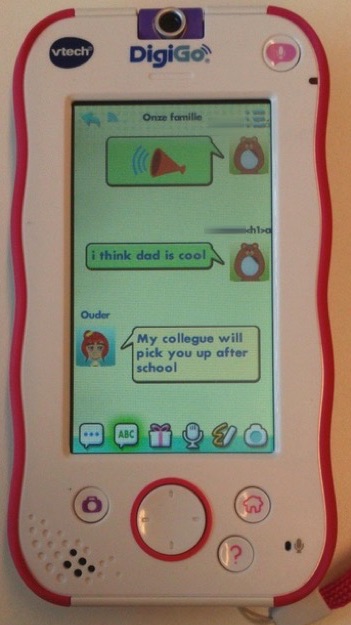
The following three screenshots show a scary Proof of Concept where an attacker hijacks a message to change the text sent from a parent to the DigiGo.