Abstract
A DLL side loading vulnerability was found in the .NET Framework version 4.6 when running on Windows Vista or Windows 7. This issue can be exploited by luring a victim into opening an Office document from the attacker's share. An attacker can use this issue to execute arbitrary code with the privileges of the target user. This can potentially result in the attacker taking complete control of the affected system. If the WebDAV Mini-Redirector is enabled, it is possible to exploit this issue over the internet. This issue can be exploited even if the Office document is opened in Protected View.
See also
- CVE-2016-0148
- MS16-041: Security Update for .NET Framework (3148789)
- OfficeDLLhijacking.zip
- Matthias Kaiser on Twitter
- Microsoft PowerPointViewer Code Execution
Tested versions
This issue was successfully verified on Vista running Office 2010 and .NET 4.6.81.0 & Windows 7 running Office 2013 and .NET 4.6.1055.0.
Fix
Microsoft released MS16-041 that fixes this vulnerability.
Introduction
Windows 7 introduces the concept of API Sets, DLL files that export functions of many well-known Win32 APIs. New API Sets are introduced with each version of Windows. It was discovered that the .NET Framework version 4.6 tries to load an API Set DLL that is available on Windows 8 and later. If .NET is installed on a previous version of Windows (eg, Vista & Windows 7), it will still try to load this DLL despite the fact that it is not available on that version of Windows. This introduces the possibility for an attacker to side load that DLL in order to execute arbitrary code. It was found that when Office is started it will also load .NET, which triggers this issue.
Details
This issue exists in the InitAppXRT() function. Before .NET 4.6 this function would check the APPX_PROCESS environment variable, after which it loads WinAppXRT.dll or kernel32.dll based on the existence of this environment variable. Loading of the DLLs is done using LoadLibraryExW() with dwFlags set to 0.
In .NET 4.6 InitAppXRT() will always try to load the DLL api-ms-win-appmodel-runtime-l1-1-0.dll (instead of either WinAppXRT.dll or kernel32.dll). dwFlags is still set to 0. api-ms-win-appmodel-runtime-l1-1-0.dll is a new API Set DLL introduce in Windows 8. On Windows versions before 8 this DLL is vulnerable to hijacking.
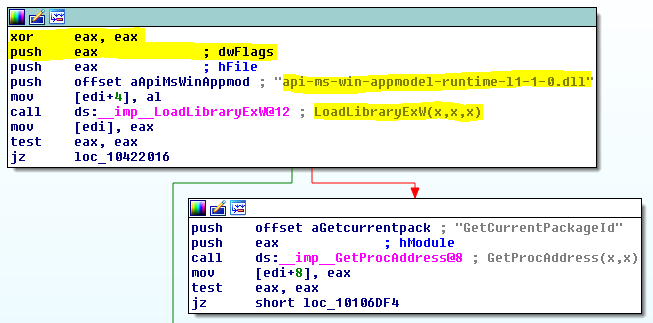 Figure 1:
Figure 1: api-ms-win-appmodel-runtime-l1-1-0.dll loaded from a relative path
One possible attack vector is Office, which loads the .NET Framework when started. Opening any Office document on an affected version of Windows will cause Windows to search for api-ms-win-appmodel-runtime-l1-1-0.dll in the current working directory. An attacker can exploit this issue by convincing a target user into opening an Office document from a directory containing the attacker's DLL. This allows for the execution of arbitrary code that will be executed with the privileges of the target user, potentially resulting in a full compromise of the affected system.
If the WebDAV Mini-Redirector is enabled, it is possible to exploit this issue over the internet. This issue can be exploited even if the Office document is opened in Protected View.