Abstract
A persistent Cross-Site Scripting (XSS) vulnerability has been found in WordPress. An attacker can create a specially crafted image file name which, when uploaded in WordPress, injects malicious JavaScript code into the application. An attacker can use this vulnerability to perform a wide variety of actions, such as stealing victims' session tokens or login credentials, and performing arbitrary actions on their behalf.
OVE ID
OVE-20160724-0018
See also
- CVE-2016-7168
- WordPress 4.6.1 Security and Maintenance Release
Tested versions
This issue was successfully tested on WordPress 4.5.3.
Fix
This vulnerability is resolved in WordPress 4.6.1 (Release Notes).
Introduction
WordPress Media Upload functionality is used to upload image, audio, video and other allowed file extensions. The uploaded media types are automatically available to public users via so called public 'Attachment Pages'.
Details
WordPress performs insufficient validation on the file name of uploaded media types and in specific images. The file name of an image is used as image Title (meta) in so called ‘attachment pages’ (HTML). An attacker can exploit this vulnerability by crafting an image file name with Cross-Site Scripting payload and lure an admin into uploading the image with the malicious file name.
Limitations
Operating System
Please note that the WordPress admin (victim) needs to use an operating system like for example Mac or Linux. These provide extended file name capabilities necessary for an attacker to be able to successfully use this vulnerability.
Social Engineering
For the attack to succeed the following conditions have to be met:
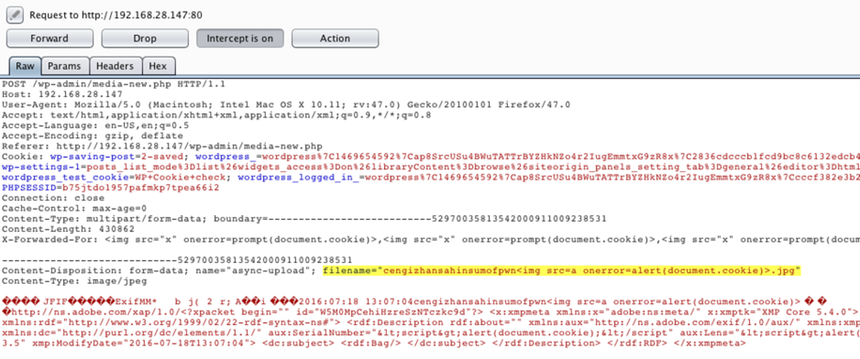
- A WordPress admin uploads a malicious image file requested by a user this admin trusts or a popular malicious image that was spread via social media. This involves social engineering. In the Proof of Concept the file name
cengizhansahinsumofpwn<img src=a onerror=alert(document.cookie)>.jpgwas used. - An attacker can now determine if the file name with which the malicious file is available on the WordPress site. With this information he can spread the URL to end users and the WordPress admin.
Proof of concept
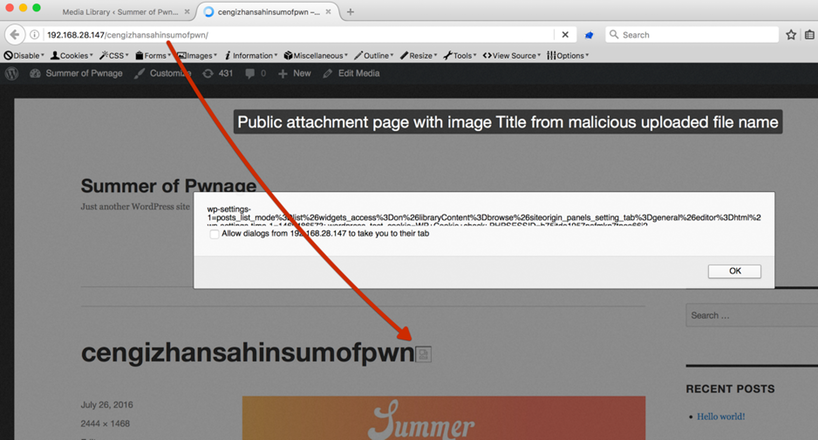
When an image with a file name such as cengizhansahinsumofpwn<img src=a onerror=alert(document.cookie)>.jpg is uploaded and viewed within WordPress the script code is executed:
The file name is always equal to the attachment page: